
Hi folks, today we’re going to talk about websites. I think that all of us knows the importance of pick up an SSL certificate for our sites. Google and web browsers, if we don’t have one, marks our sites as unsafe, the websearch are not well indexed in an unsecure site. In this article we’ll learn how to create an SSL certificate in our PC.
Contents
What is an SSL certificate?
SSL is a global security standard that allows websites and servers to transfer data securely reducing the risks of data theft. This secure connection between our website and the server is made using an SSL certificate.
An SSL certificate can be issued by different certification authorities (CA), like Verisign, ZeroSSL, and Let’s Encrypt, among others. In this article, we’ll talk about certbot, a command line tool that fetches certificates from Let’s Encrypt.

Let’s Encrypt is a non profit certificate authority (CA). Launched by the Electronic Frontier Foundation (EFF), Mozilla Foundation
Environment and settings
The only thing that you need to do is install certbot from your Linux software repos or follow the instructions
SSL certificate: create it to use in website’s hosting.
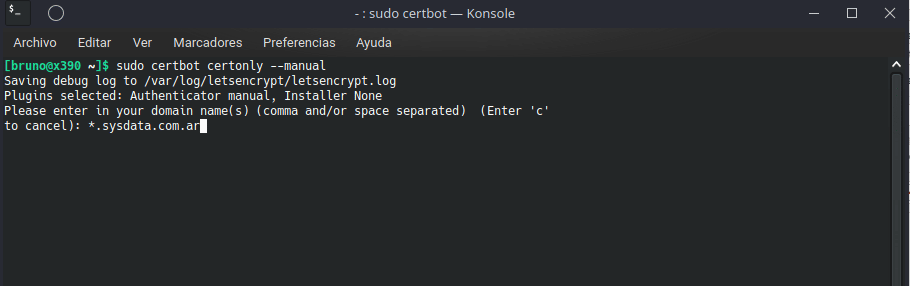
Here we will see in detail how to create an SSL certificate from a GNU/Linux machine, for use later in another server machine, or even in a website’s hosting like Bluehost, Hostgator, etc. The command line syntax for certbot is really simple, and you only need to do the following:
sudo certbot certonly --manual
We need to enter the domain name, with and without www, and subdomains separated by commas. Also, you can obtain a wildcard SSL certificate. A wildcard certificate will work with domain and all the subdomains. In this example, we’ve used the syntax to obtain a wildcard certificate.
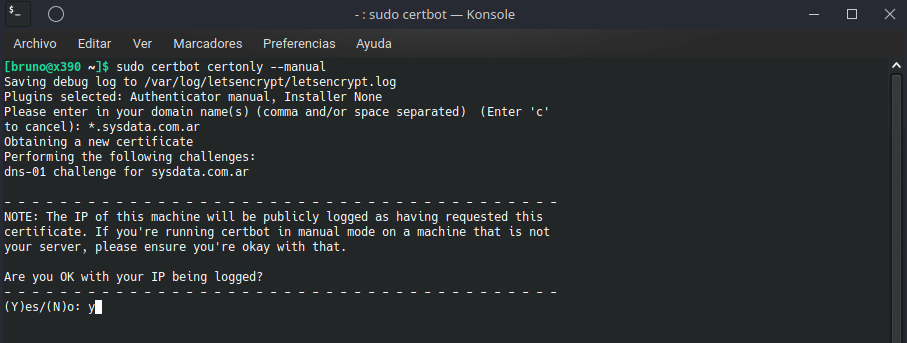
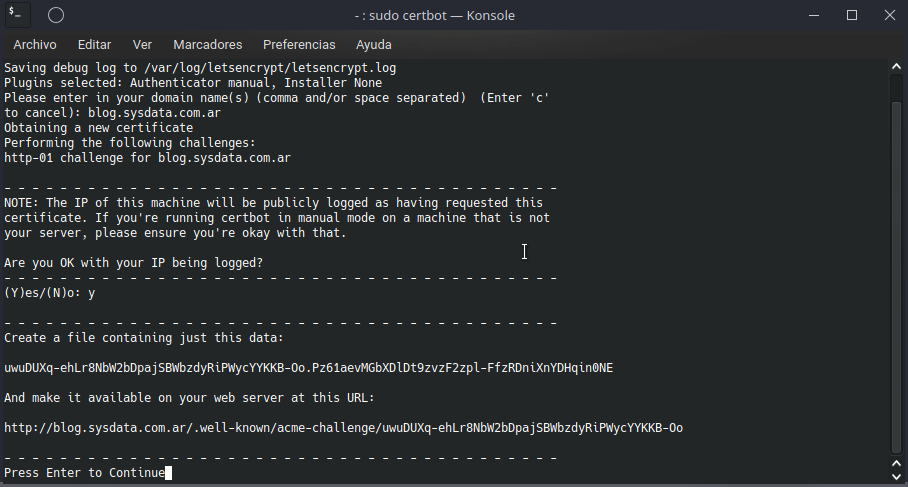
In the next image, you only need to answer yes. This is because we’re creating an SSL certificate for other server rather than the machine that we’re using.
At this point we need to create a DNS TXT registry in our hosting panel. Plesk, Cpanel and others have an option under domain menu option.
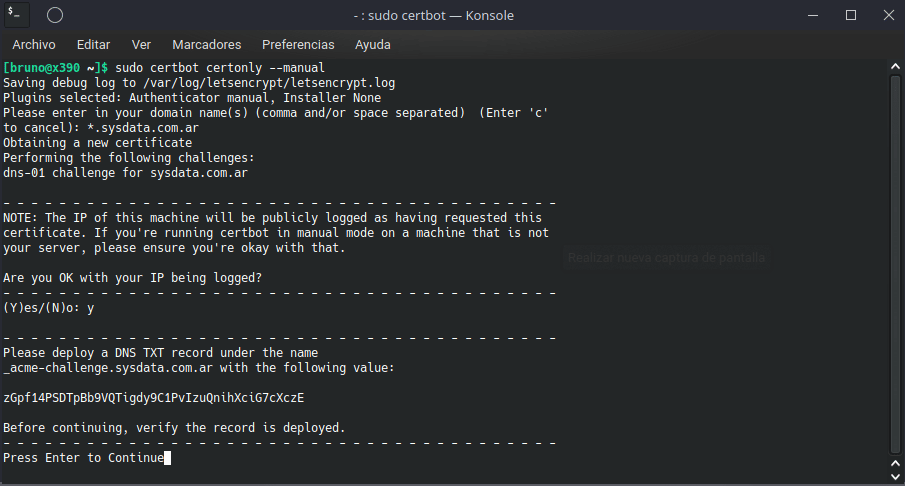
Once created, press enter and certbot will check that entry and finishes the creation process. You will find your brand new certificate under /etc/letsencrypt/live/domainname directory.
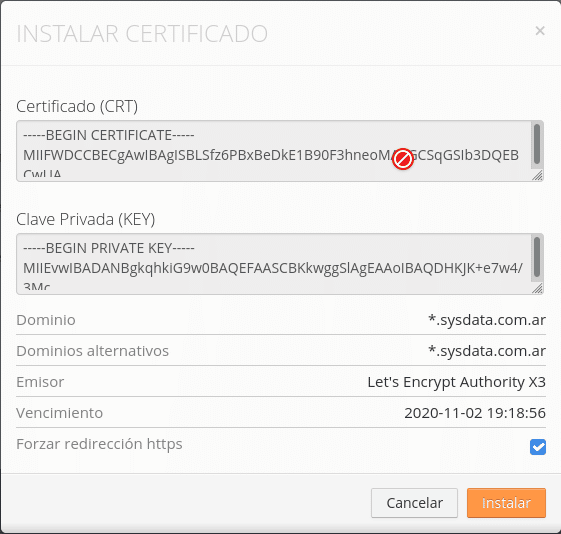
The last thing to do, is copy our certificate and private key in the SSL/TLS options, usually under domain menu. It’s done, now we’ve our site secured, principal domain and all the subdomains.
We need to renew our SSL certificate every three months and we do that using “sudo certbot renew” order. By executing “sudo certbot certificates” we can see all the SSL certificates present in our machine.
If we don’t use a wildcard certificate, the options are quite similar, but we need to do a classic acme-verification in order to probe the ownership of the domain. Certbot will give us instructions to create a file with some content, and put it in our public_html root folder and make it available.
As in wildcard example, we need to export the certificate and private key under SSL/TLS options.
Why use an SSL certificate?
An SSL certificate protects the information and data sent over the internet using an encryption process preventing data theft, phishing, and other security threats.
We can identify secure sites very easily. In the address bar you will see the padlock if you’re browsing in a secure website and you can see that the webpage uses HTTPS protocol.
Final thoughts
As you see, is quite simple and really important to secure our sites. If you do it manually, you don’t need to pay any additional for this. As a con, we need to renew the SSL certificate every three months. If you have a dedicated server, you only needs to do the process one time. Certbot will do the stuff automatically.
See you next time!
1 thought on “How to create an SSL certificate with certbot”